Single Sign On to the Game Portal Spellenmug
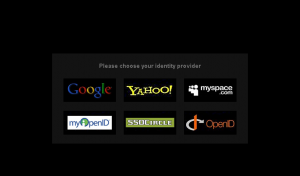
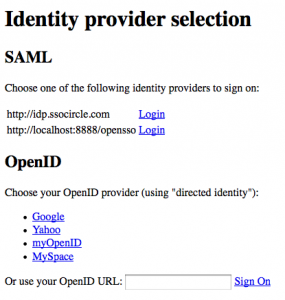
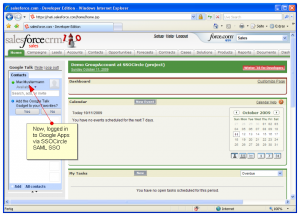
The board game portal www.spellenmug.nl offers several options for single sign on. Most of them are OpenID based. Only one leverages SAML v2: the only free, open and public SAML V2 Identity Provider SSOCircle.
SSOCircle IDP has now more than 250 integrated SAML v2 service providers in its SSOCircle of trust. Although many of them are developing and testing applications and some do not allow us to use them as a reference, we believe that this is one of the largest and most active circle of its kind.