Configuration and Metadata Certificate Changes
Applies to the Public IDP. Not to our IDPee offerings.
Update: Public IDP Metadata will be replaced during a maintenance window at the weekend of 13/14th August 2016. We do not expect downtime but there may be some changes needed at your service provider.
SSOCircle Root CA certificate used for client certificate authentication will also be replaced in the first week of August.
Details on the changes:
- Replacement of the SSOCircle Root CA Certificate
- SSOCircle Public IDP Certificate and its SAML Metadata will be replaced. The certificate will be signed by the old SSOCircle CA certificate. The SAML Metadata and the endpoints itself are considered deprecated.
- New Public IDP Metadata will be introduced with new endpoints, new keys and certificates signed by the new SSOCircle CA. The new Public IDP Metadata should be used with new deployments and should replace the old metadata.
- Client certificates used for strong authentication when signing in to the IDP will now be signed by the new SSOCircle Root CA certificate. Old certificates will continue to work
What you need to change:
Details depend on your SP implementation and configuration. The following points should only direct you into the right direction.
Deprecated use of old IDP Metadata (may be removed in future)
During the weekend of 13/14th August replace the SSOCircle IDP certificate in your SP configuration with the new certificate or just replace the metadata (if your SP supports SAML Metadata)
Deprecated SSOCircle Public IDP Metadata
Recommended: Use of new IDP Metadata
From now on, you can use the new IDP Metadata (If your SP supports SAML Metadata)
SSOCircle Public IDP Metadata
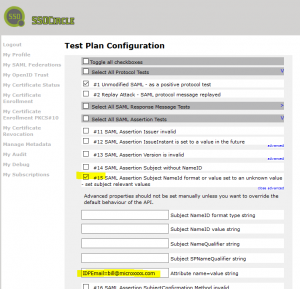
If you need to change your SP configuration manually, you need to change the certificate and properties as listed in IDP Configuration Changes.
SSOCircle Root CA Certificates can be found at the URL:
SSOCircle CA Certificate
SSOCircle CA Certificate (deprecated – legacy use only)