SAML 2.0
For detailed information please consult the OASIS website.
The intension of the following description is to explain SAML in the Web SSO context used at
SSOCircle.
Sharing of security information between two web sites are based on a common understanding of how to refer to an user and how to exchange statements about this user. The communication protocol must define the (network)way of message exchange (e.g. SOAP over HTTP), the request and response scheme (e.g. authentication request for user A), the content and how requests and responses are formatted. And last but not least it must describe security aspects of the exchange.
One way of standardization of these requirements is achieved through the OASIS SAML v2.0 specification. SAML v2.0 is an advancement built on SAML v1.1 which also incorporates input from Liberty Alliance’s Identity Federation framework.
SAML describes network protocol bindings, assertions and request/response protocols.
Network protocol bindings:
SAML defines the wrapping of messages into SOAP over HTTP.
Assertions:
Assertions are expressed in XML and mainly consist for example of the user information (subject) and a statement about the user. A statement can consist of authentication and/or authorization information and include additional attributes of the user’s profile.
Request/Response protocols:
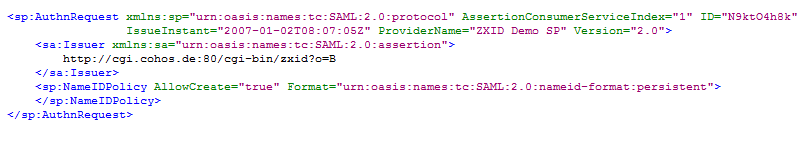
In order to receive specific assertions queries are defined. For example to get an authentication assertion about a user a web site can send an authentication request (AuthNRequest).
Profiles:
In addition to the network- and SOAP-binding and the way how requests/response must be constructed information is needed of how to transfer the messages. For this purpose SAML specifies profiles. For example the Browser POST Profile describes that SAML requests/responses are sent through the body of a HTTP-POST request.
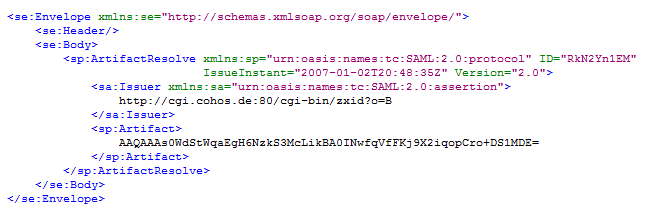
The Browser Artifact Profile specifies an identifier called “Artifact” that can be used by the other website to query information about a user via a dedicated SOAP back channel.
Artifact Resolve request:
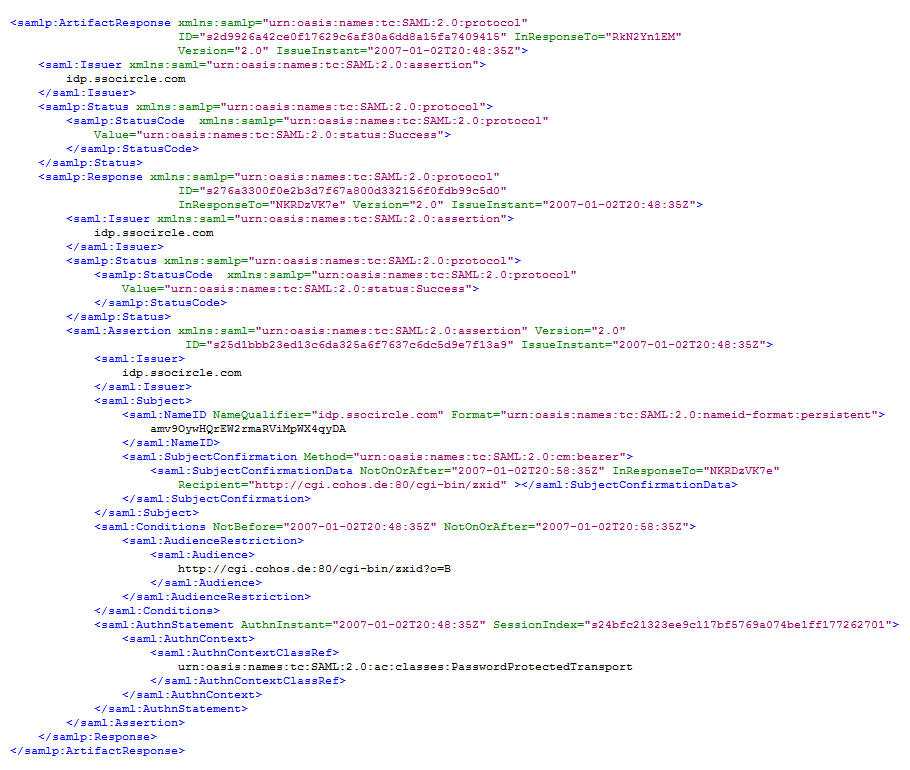
 Artifact Response:
Artifact Response:
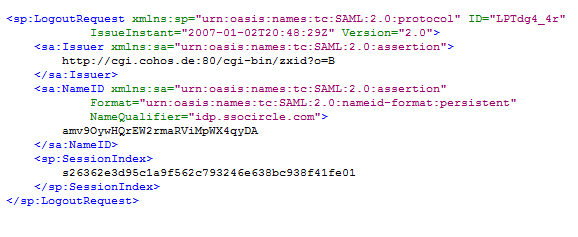
Other profiles describe for example how to accomplish a Single Logout, how to discover an identity provider in the case where more than one is defined.
LogoutRequest:
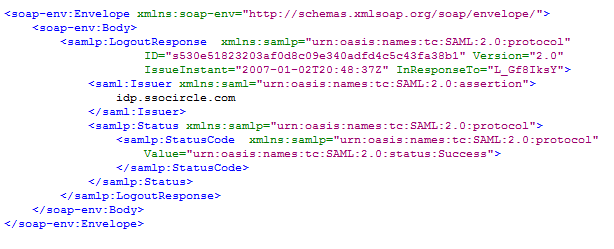
 LogoutResponse:
LogoutResponse:
Roles:
Roles defined are:
Metadata:
Metadata is used to define the format of information that is needed for one party to communicate with the other party. Examples are URLs of specific services and certificates that are used to sign and encrypt the data. If one party joins a Circle of Trust metadata must be exchanged between the communicating parties.
There are several other topics which are described in the SAML 2.0 specification. The interested reader is referred to the complete specification at the OASIS website.
